Combining VeraCrypt, Google Backup & Sync, and Sql Server Part 1
2018-01-04 18:00
This is a two-part post. Read Part 2 here.
It's important to protect business data. Employee access and use of data should be managed by the IT department. But a contractor is often entrusted with data on their own computers. We certainly don't want our laptop to be stolen and have to tell the client that source code or databases with sensitive data just got lost, and, no, it wasn't encrypted.
Below, I discuss how I used VeraCrypt for my encryption. In Part 2, I show how I solved problems relating to Google Backup and Sync, and Microsoft SQL Server.
For Windows users, there are a few encryption solutions.
BitLocker
BitLocker is available on these editions:
- Ultimate and Enterprise editions of Windows Vista and Windows 7
- Pro and Enterprise editions of Windows 8 and 8.1
- Pro, Enterprise, and Education editions of Windows 10
- Windows Server 2008 and later
To use BitLocker, your computer hardware must have a compatible Trusted Platform Module.
I won't go into how to configure BitLocker. Suffice to say, if you have this option available, I think you should use it unless you have a reasonable security objection. And if that's the case, you're already looking into alternatives.
I do not use BitLocker because my hardware doesn't support it.
Windows Encrypting File System (EFS)
EFS is available on all Windows editions from 2000 onward, Professional and above. When configured, decryption happens transparently. It's important to export and separately store the encryption password. There are security issues with EFS, but for my purposes I thought it would be an acceptable solution.
I tried setting a client folder to use EFS, but ran into a significant problem: a showstopper, in fact. If found that I couldn't create a new Visual Studio ASP.NET project from a template.
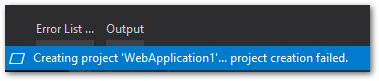
Since I'm primarily a web developer, this simply wouldn't work.
More Information
If you want to read more about BitLocker and EFS, try this article.
VeraCrypt
VeraCrypt is the successor to TrueCrypt, which I used many years ago before the author abruptly shut down the project. VeraCrypt has been security-audited, and I'm glad to be using it (again). It can be installed on any edition of Windows, as well as Linux and Mac OS X.
VeraCrypt has two main configuration scenarios:
- Using a container file, create a virtual encrypted drive with its own drive letter.
- Encrypt an entire partition or drive.
Arguably, as with BitLocker, the best thing to do is encrypt the entire drive and deal with the extra passphrase prompt when booting up. However, I opted for the quicker option of container file.
VeraCrypt Walkthrough
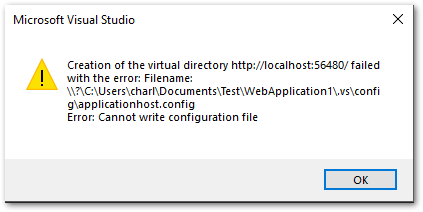
Here's a simple walkthrough to install and configure VeraCrypt the way I did.
Download and install the latest Windows version.
Open the application and click Create Volume
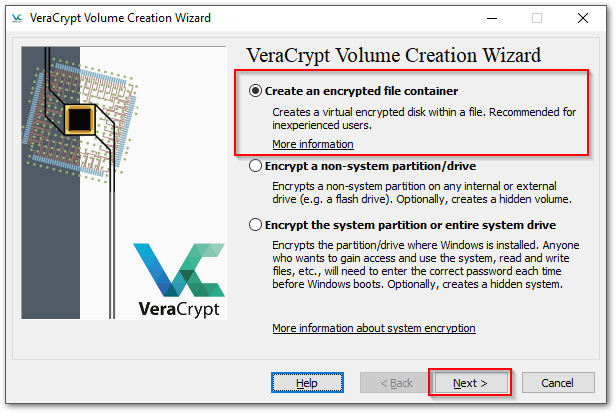
Choose "Create an encrypted file container" and Next.
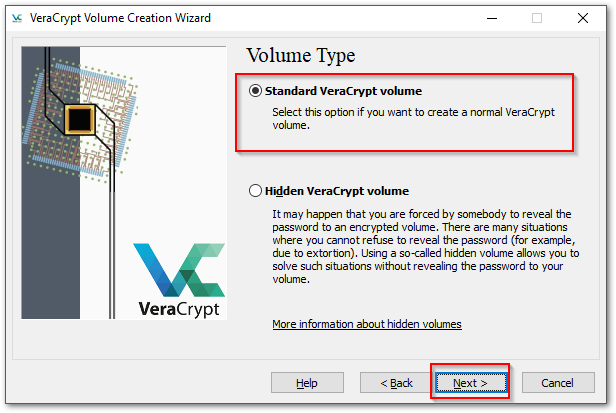
Choose "Standard VeraCrypt volume" and Next.
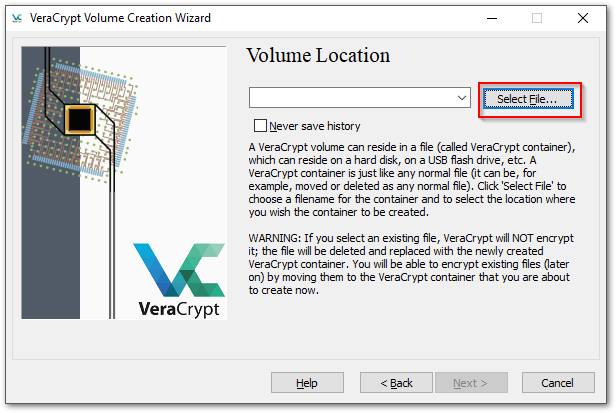
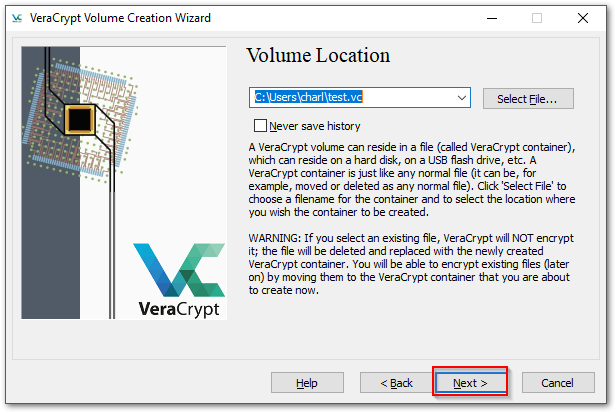
Enter a new filename and path, which you can also set via the dialog. It doesn't matter what the filename or extention are. It doesn't even need an extension.
Warning
If you choose an existing file, it will be overwritten. Don't do that. Create a new filename.
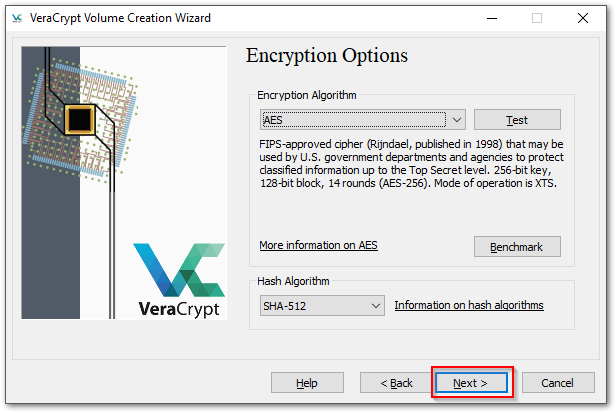
Choose your encryption options. The defaults are fine.
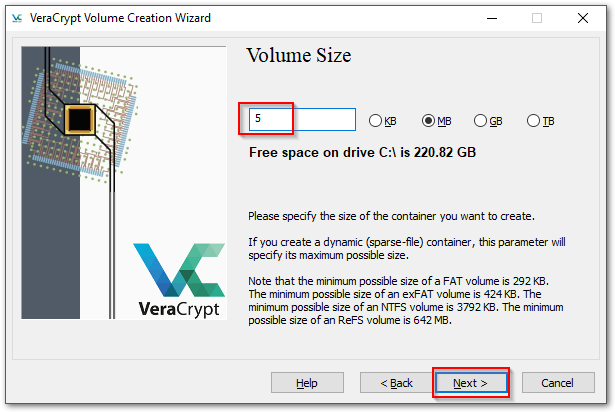
Choose the maximum size of the drive. Remember, any size you choose here subtracts from your available physical drive space. If you ever need a larger encrypted drive, you'll need to create one and move all the files. For this exercise, choose 50MB.
Note
I know the screenshot shows 5MB, but it needs to be higher to create the database later.
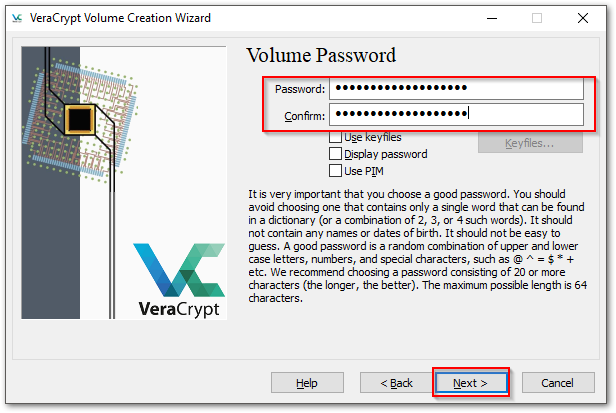
Enter your password or passphrase. I like passphrases, because they can be long but easy to remember. Here's one:
MyBoatDripsFeathers
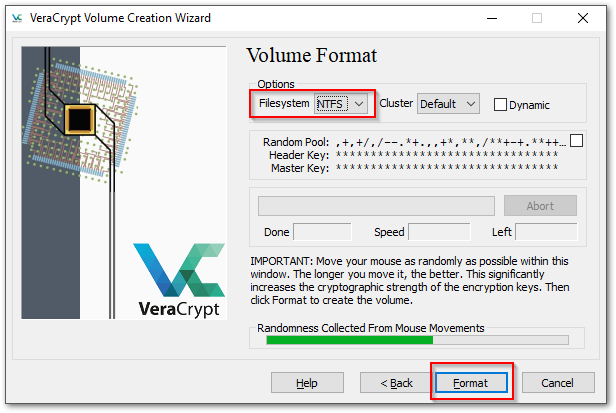
Choose the NTFS filesystem, then start moving your mouse around until the bar turns green. Click Format. I'll take awhile, depending on the size of the drive, and you'll be prompted by Windows to allow it.
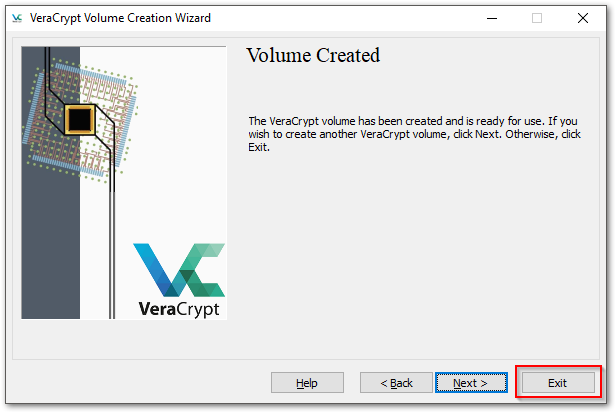
Exit the wizard.
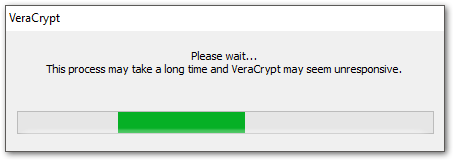
You've configured the container file that will hold your encrypted data. Now you'll mount the file. In the main window, choose the file you just created, select a drive letter, and click Mount. The file will be mounted and you'll have a new Windows drive letter.
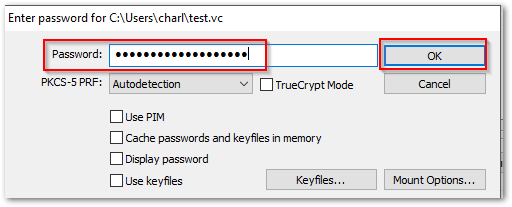
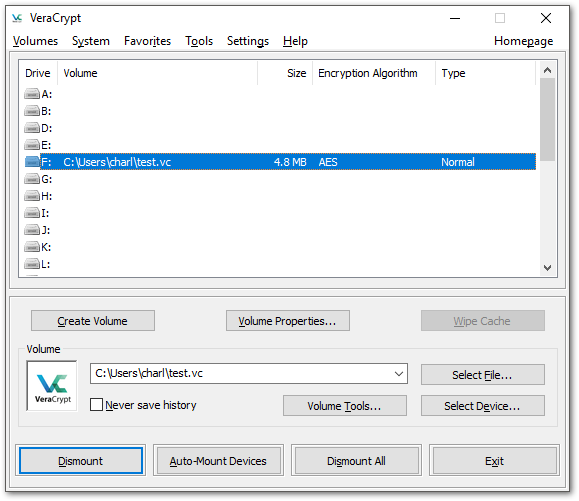
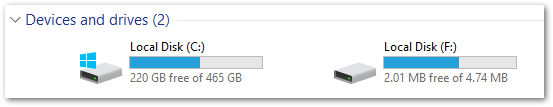
Now, any files you add to the F drive are encrypted. If someone were to steal your machine, they'd have to know your Windows password and your test.vc password. If they pulled out the the hard drive and installed it on another computer, all they'd see is a file named test.vc amongst all the other files, and they couldn't open it without VeraCrypt and knowing the password.
The F drive is only available when you're logged in, and when you log in fresh you must start VeraCrypt and mount test.vc.
